Defeating phishing emails and securing your inbox
This post is part of a series contributed by the ISO’s 2019-2020 student intern Emily Connolly, ’20.
It’s 8am on a Monday morning. You pour yourself a cup of coffee and open your laptop to read all the emails you’ve been putting off since Friday afternoon.
When you open your mail inbox, this message is waiting:
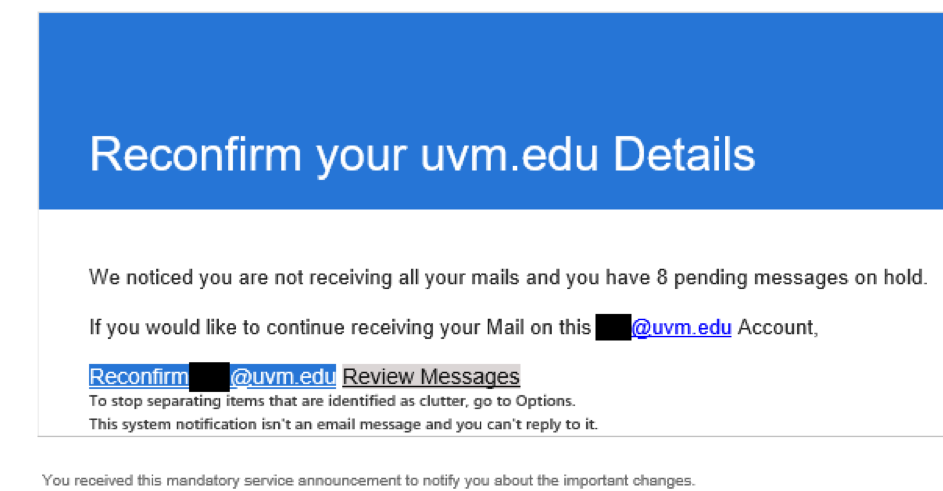
“Oh no!” you think. “Have I not been getting my emails? What does this mean?”
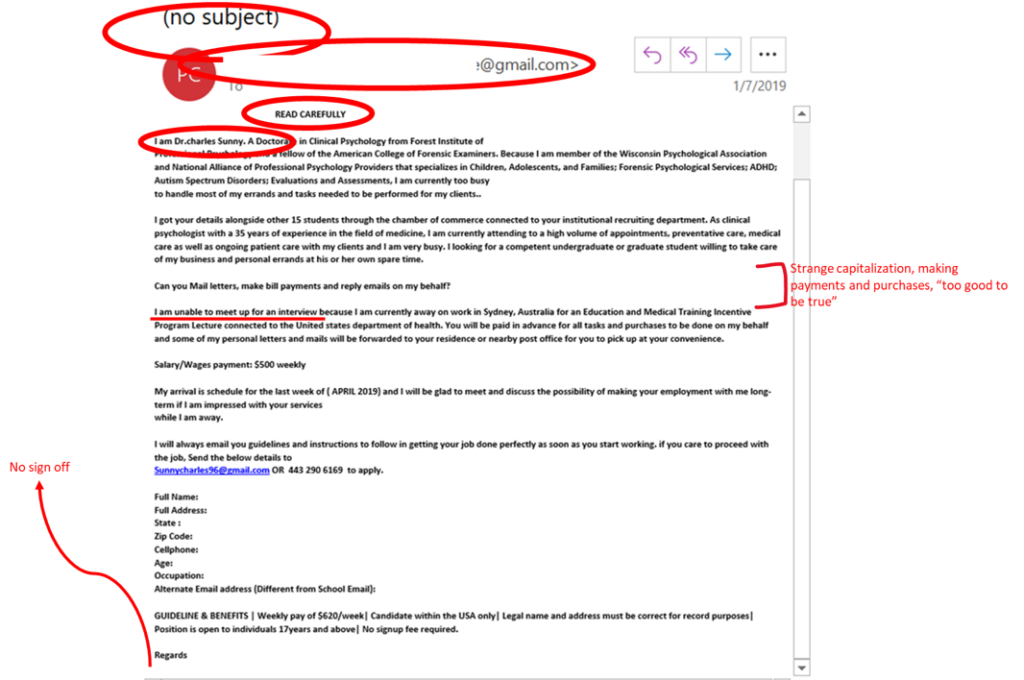
Before doing anything, however, it’s important to consider the threat of a phishing scam— an attempt to steal your UVM credentials (your NetID and password). A phishing scam often comes in the form of an email, perhaps one asking for you to enter your UVM credentials or offering a well-paying part-time job from a professor working overseas.
Often times, phishing scams will try to play off your emotions—such as a mail message threatening to delete your account, the idea of an easy side job, or a compromised UVM NetID. The goal is to get you to act fast, getting you to enter in your UVM credentials to solve the problem quickly without noticing the signs that the email you received isn’t actually legitimate.

Here are some things to look for when you see a suspicious message:
- Check the email subject. Has it been left blank? Is it vague? Does it use a “scare-tactic” to get you to act fast? Do you feel pressured?
- Who is it being sent by? Is it not a UVM email? Is it someone you don’t know? If it is someone you know, is it a strange request for them to have?
- Where are the links going to? Any email that asks you to enter your UVM password on a non-UVM web site is a phishing scam. UVM will never ask you to enter your UVM NetID and password on a non-UVM web page—even if it looks like a UVM page, and even if it’s on a reputable site, such as Google Docs, or if it contains UVM graphics and you’ve been directed there by an email that appears to come from a UVM email address. Remember: The UVM Tower logo or any related graphic is not a guarantor of legitimacy.
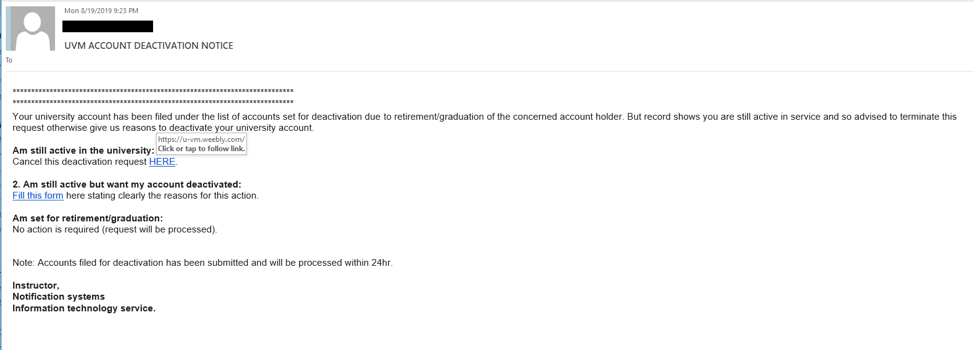
For example, this email here is directing users to a Weebly site, and by mousing over the link, you can see where the link will take you without clicking.
- Does the email have strange capitalizations or odd grammar and spelling? Is there no greeting or sign off? Does the signature not match the email sender?
- Is money involved? Do they want me to help them pass checks or move money with the promise of payment afterward?
- Ask your friends. Does the email seem like a scam to them? Sometimes, taking a step back from the situation can help you think more clearly.

If you’re even unsure about the legitimacy of a message, you can contact the Computing Help Line at 656-2604, or submit a help request online. You can also directly contact the party involved by directly mailing the organization or office the email is purporting to be from, but not by replying to the suspicious email. Instead, use the email you have on file for the organization or the one they display publicly on their website.
You can also report phishing emails by forwarding the phishing email with full headers to abuse@uvm.edu. (To forward a message with headers, please see https://www.uvm.edu/it/kb/article/forwarding-full-mail-headers)
What to do if you’ve fallen for a phishing scam

If you’ve followed the link in the message, or replied to this email or one like it, you should change your password immediately at www.uvm.edu/account. Contact the UVM Computing Helpline if you need assistance changing your password. You should also change any similar passwords to your UVM password.
More info
For more information about phishing scams, view our Web page on protecting your NetID and password.

